Achieving true privacy online is difficult. Within this piece I will discuss a few ways you can reclaim some privacy and better protect yourself from malicious activity.

Once upon a time, the internet was viewed as a private place, but modern digital life today is quickly overpowering any feeling of privacy we have online. The internet can peek into the most private spaces of our lives. Once it’s online, it’s there forever. Online privacy has now almost become non-existent, giving data thieves more potential to run amok in everyday transactions, social media interactions and web searches.
And while it’s no longer possible to go back to the days where there was no such thing as surveillance, here are a few steps that will help you stay hidden on the web, lessen the amount of spam and ads you encounter, and generally just have a better time online:
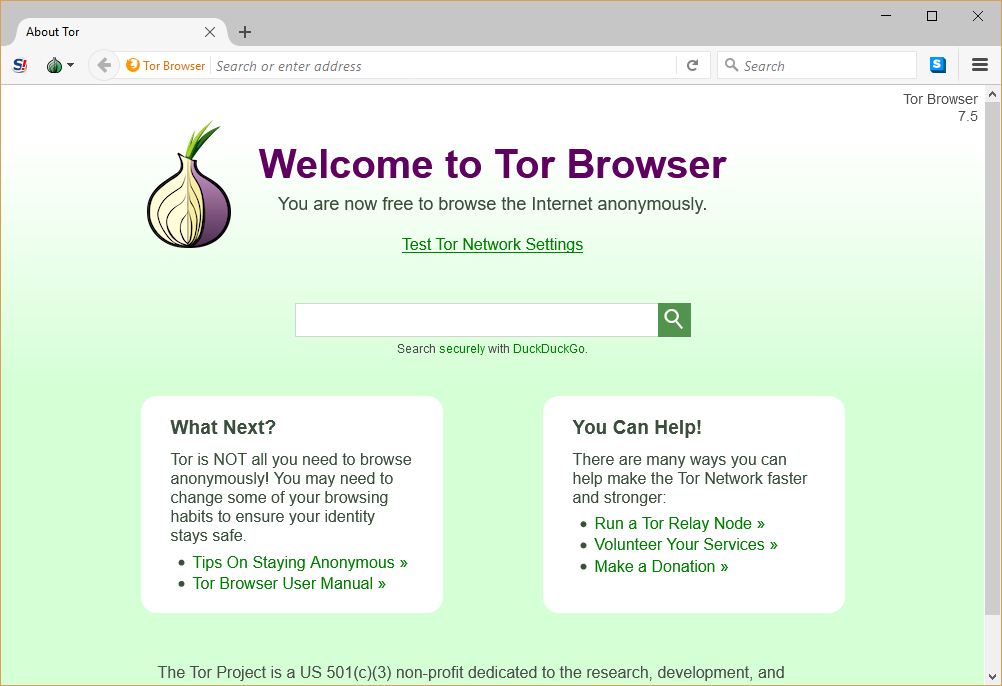
Using Tor
The Tor browser is a Firefox fork with some changes concerning privacy. The browser is not the only way to access Tor, but rather is a convenient plug and play solution that offers reasonably good privacy protections over a regular browser, and is preconfigured to connect to the Tor network out of the box.
Tor consists of thousands of relays, otherwise known as nodes, located across the world. The Tor network is supported by volunteers who keep it open to everyone, free of charge.
Every time you use Tor, all the data that gets uploaded and downloaded during that period is encrypted and sent through a random sequence of nodes. This random sequence is next to impossible to track back to your computer, this process is known as onion routing and hence Tor’s name: The Onion Router.
Tor offers more than just super-impressive anonymous properties, Tor also offers another layer of tweaks and limitations to make you stay anonymous. Here are some of them:
- As soon as you quit the Tor Browser, your browsing history is automatically deleted
- Automatically redirects towards the HTTPS version of a particular page.
- NoScript is baked in, stopping executable scripts from running on web pages until the user manually allows it
- Tor button disables any kind of ‘active’ content at the application level, such security concerns were inherited from the button originally being an addon on the Firefox browser.
- Most extensions and plugins aren’t supported on this browser—this might cause some browsing hiccups but also significantly reduces your chance of malicious (or compromised) third-party apps ruining your day
- It fixes your non-maximized window size to a standardized size common across all tor installations. Keeping it this way and not maximized won’t allow sites to use your screen resolution as a data point for uniquely identifying you. There are several standard resolutions, and the actual content area vertically is usually slightly different for everyone’s configurations. A significant majority of people in the US can be uniquely identified with just their first name and date of birth or by date of birth, gender, and ZIP code (or broader), so it stands to reason that users can be uniquely identified with just a few data points about their device and browser configuration for purposes of data mining.
It’s important to remember that the Tor browser is a self contained unit, and only uses the Tor network for traffic inside the browser. Therefore, it won’t anonymize activity carried out by other programs like BitTorrent, or other share software media players. However, it is possible to route those programs through the Tor network. Since the Tor browser isn’t supported on mobile devices, it’s recommended Android users download Orbot.
Tor also allows users to connect to .onion sites, which are one layer of the so called “Dark Web.” Many of these sites are perfectly normal, and simply don’t exist on the typical layer of public internet routing, but many are also places for illegal content or services.
This subject is where Tor suffers from a problem for daily use: a lot of spam or illegal activity is routed through Tor, and not only have governments kept a close eye on it (and have compromised it from the inside before), but many sites will block Tor connections, or at least provide a captcha you may not have otherwise received to access the site at all.
For that reason, it’s not the ideal solution for the standard user seeking another layer of reasonable privacy protection. If you’re not trying to protect your data from state data requests, then there are far better and faster solutions out there.
Avoid Popular Search Engines
The usual suspects! Google, Bing and Yahoo will collect most of your data to serve relevant ads and personalized services. Especially when logged into your browser account, search engines can collect your name, email id, birthday, and other critical data. Other than that, Google and Bing can also collect data such as your device location and IP address. If you’re trying to avoid being tracked while searching on the web, you can easily use a service like DuckDuckGo. DuckDuckGo is an independent search engine that doesn’t give you any custom search results. All people see the same results, and anything you search won’t be collected or stored. The search engine also claims that it has nothing to do with advertisers, and it won’t ever be subject to targeted ads using Google or other websites.
Using an anonymous VPN
You can also use a virtual private network (VPN). Generally the browser sends a query tagged with your IP each time you make an online search, and this IP is then viewed and monitored for its data—including your personal information and IP address. In the case of a VPN, your identity gets changed because it is assigned by your anonymous VPN. Therefore, the query you are sending to your ISP would be encrypted and therefore your actual IP won’t be displayed any longer.
Using Privacy Plugins
There are several popular plugins that leave clues about your identity and location. Even advertisers and third-party trackers are tracking your web browsing. If you need to preserve your anonymity, then you need to use plugins like Privacy Badger that is available for Chrome and Firefox. It can watch third-party domains that places images, scripts and advertising in the web pages you visit, and stops them from tracking you. Once you’re on a website, you can see a list of all the trackers found in it. Each of the trackers are shown as green, red or yellow: green is for those that appear to be safe, red signifies those where add-ins are completely blocked, and yellow for those that are partially blocked. The more you browse, the more effective Privacy Badger becomes, as it is a self-aware system that learns over time.
Cleaving to HTTPS
Using HTTPS is important for trying to prevent a third party from accessing the material you send to a website, but the website itself will always have what you submit to it as well as info info they receive on their end, like the IP of the endpoint you use to connect and anything your browser sends.
Setting up anonymous burner accounts
While you would need an entirely different set of password and password question answers for each website as you create a login account. These ‘burner’ email accounts are expendable and make it much harder to track your real identity. Use email services which explicitly advertise anonymity, and have both free and commercial versions. Once you connect to them using any other anonymous apps and connections, and switch among burner accounts, you’ll be far less detectable. Sites like Guerilla Mail set up an email that only lasts for 60 minutes before self-destructing
Keeping safe and updated
- Always use an antivirus. Regular scans and real-time monitoring can go a long way in ensuring protection from malware.
- Enabling your firewall as it is one of the best defenses against unsolicited connections
- Secure the wifi router.
- Secure your webcam
It is highly crucial to keep all your apps and operating systems updated at all times. If you are putting off updates, which consists of security patches, you become a lot more vulnerable to data theft and hackers. I know it can be a pain, but it’s the simplest thing you can do to keep out malicious code—companies are generally very good at responding after vulnerabilities have been discovered but they’re not psychic. Updates are often their response to a new vulnerability, and neglecting them will leave huge holes in your security.
To sum things up, true online privacy is hard to come by. In times like these when your identity can be attacked from all sides, it’s important to be in the know and act accordingly.
If there’s anything this article states, it’s that in modern business, you can’t be slack when it comes to security. If you’d like to optimize security on your website, it’s worth getting in touch with our development team at CodeClouds. To start with, read our security tips to keep your website protected.